
Secure web browser access
Cybersecurity threats are among the main risks facing asset managers today. Older hosting models, such as on-premise or managed hosting offerings, are especially at risk as potential attackers get more sophisticated.
True cloud solutions, on the other hand, are significantly more secure, helping investment managers improve governance. You can sleep well at night with Limina, a cloud-native Investment Management Platform running on the world’s most secure cloud, with best practices and cutting-edge safeguards.
Enterprise SaaS for investment managers takes security one step further
As a cloud solution provider, ensuring security, privacy, and control is paramount and a responsibility we don’t take lightly. While cloud solutions enable a much more robust security setup than traditional solutions, security is a multi-faceted topic that expands beyond the scope of technical solutions. Security stands as a fundamental priority for Limina, encompassing our people and processes. We fortify your IMS against external threats, system faults, manual errors, and bad actors.
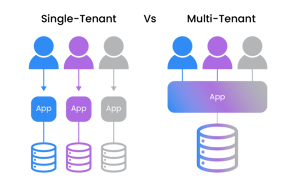
Limina’s solution is built for enterprise use cases, so we take security one step further than other cloud providers. For example, we partition data separately for each client – called a multi-instance data model. With such separation, even in the improbable scenario that one client’s environment would be breached, this would be isolated to that client and not affect any of our other clients.

How we work to secure your environment
Naturally, we won’t put everything we do to protect your environment on our website for security reasons. Some examples of how we work with security include:
- Automated intelligent threat detection services from AWS
- Automated backup management, including redundant storage and encryption of all data at rest
- Managed services from AWS for general service availability (incl. database and network)
- Highly restrictive role-based access to servers (Zero-Trust Policy)
- Best-practice system architecture (multiple security layers)
Advanced permission system in the application – granular permissions configured per user or user group level - Audit trail for all data changes
- Compliant with GDPR
- Compliant with data locality requirements (e.g., EU data saved in EU data centres)
- Secure login: You can enforce Two-factor authentication (2FA) or Single-Sign-On (SSO) for the whole organisation
- HTTPS - Secure HTTP connections over TLS
CURIOUS TO LEARN MORE?
Don't hesitate to get in touch - we're happy to advise on any questions you may have about the product and how it can fit into your landscape and support your target operating model.








